Originally published by nvk 🌞 @nvk on X.
View original article
· View original post
· 2026-04-06T14:35:54.000Z
“I” Spent “200” Hours Reading Quantum Computing Papers So You Don’t Have To. Bitcoin Is FINE.
Well, mostly fine. The truth is more interesting than the panic — and more urgent than the dismissals.
[Part 2 is now live here – The Quantum Computer That Will ‘Kill Bitcoin’…]
TL;DR for Skimmers
Bitcoin does not use encryption. It uses digital signatures. Most articles get this wrong, and the difference matters.
Quantum computers cannot “crack Bitcoin in 9 minutes.” That headline describes a theoretical circuit on a machine that doesn’t exist and won’t for at least a decade.
Quantum mining is physically impossible. It would require more energy than the Sun produces. Seriously.
Bitcoin CAN upgrade — it has before (SegWit, Taproot) — and work has started (BIP-360). But the community needs to move faster.
The real reason to upgrade isn’t quantum — it’s that classical math has broken countless cryptographic systems and secp256k1 could be next. Quantum computers have broken zero.
There IS a real concern: ~6.26 million BTC have exposed public keys. This isn’t a thing to panic about. It’s a thing to prepare for.
The Throughline
Here’s the one-sentence version of everything I’m about to tell you:
The quantum threat to Bitcoin is real but distant, the media coverage is systematically unhinged, and the most dangerous thing isn’t quantum computers — it’s complacency disguised as either panic or dismissal.
Both the “Bitcoin is doomed!” crowd and the “Nothing to see here!” crowd are wrong, in ways that are equally unhelpful. The truth requires holding two ideas simultaneously: (1) there is no imminent quantum threat to your Bitcoin — and the threat may be much further away than the headlines suggest, and (2) the Bitcoin community should be preparing anyway, because the upgrade process itself takes years.
That’s not a reason to panic. It’s a reason to start.
Let me show you the math.
Part 1: The Media Machine (Or, Why Headlines Are the Real Threat)
Every few months, the same cycle repeats:
A quantum computing lab publishes a careful, heavily caveated research paper
Tech media writes: “QUANTUM COMPUTERS COULD CRACK BITCOIN IN 9 MINUTES”
Crypto Twitter compresses this to: “BITCOIN IS DEAD”
Your uncle texts you asking if he should sell
The actual paper says nothing of the sort
In March 2026, Google’s quantum AI team published a paper showing that breaking Bitcoin’s elliptic curve cryptography would require fewer than 500,000 physical qubits — a 20x improvement over prior estimates. This is genuinely important research. Google was so serious about responsible disclosure that they withheld the actual attack circuits and published only zero-knowledge proofs.
What the paper did NOT say: that Bitcoin can be cracked today, that a timeline exists, or that anyone should panic.
What the headlines said: “Bitcoin cracked in 9 minutes.”
CoinMarketCap ran an article titled “Will AI-Accelerated Quantum Computing Break Bitcoin in 2026?” The article then spent its entire body explaining why the answer is “almost certainly no.” This is the standard pattern: sensational headline for clicks, cautious body for accuracy. But 59% of shared links are never clicked — so the headline IS the message for most people.
Raoul Pal had the best economic debunk: “Markets price risk extremely fast. You wouldn’t steal something that collapses in value the moment you take it.” If quantum computing were about to break everything, Google itself — which uses the same cryptography — would show panic in its stock price. GOOG is doing fine.
The takeaway: The headlines are the real misinformation. The research is real and worth understanding. Let’s do that.
Part 2: What Quantum Computers Actually Threaten (And What They Don’t)
The #1 Misconception: “Encryption”
Nearly every article about quantum computing and Bitcoin uses the word “encryption.” This is wrong, and the error changes everything.
Bitcoin does not use encryption to secure your funds. It uses digital signatures (ECDSA, and more recently Schnorr via Taproot). The blockchain is public by design — all transaction data is visible to everyone, always. There is nothing to “decrypt.”
As Adam Back — inventor of Hashcash (cited in the Bitcoin whitepaper) — puts it: “Encryption implies data is hidden and can be decrypted. Bitcoin’s security model is based on signatures that prove ownership without exposing the private key.”
This isn’t a semantic quibble. It means the “harvest now, decrypt later” threat — the strongest urgency argument in quantum computing — largely doesn’t apply to Bitcoin fund security. There’s nothing encrypted to harvest. The public keys that are exposed are already sitting in the open on the blockchain.
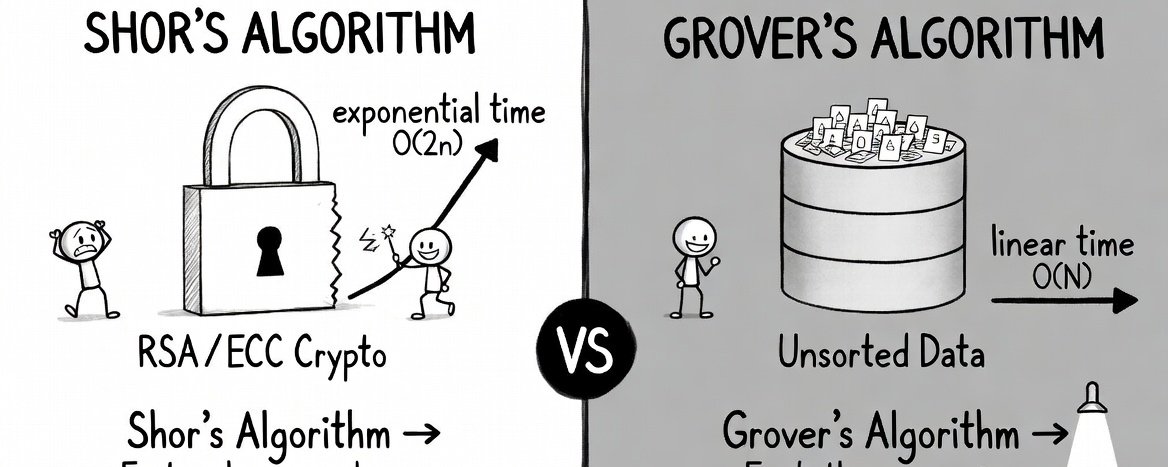
The Two Algorithms: One Matters, One Doesn’t
(Stick-figure diagram style borrowed from Tim Urban’s Wait But Why — if you haven’t read his work, you should.)
Shor’s Algorithm (the real threat): Provides an exponential speedup for breaking the mathematical problem underlying digital signatures (ECDSA). This would allow someone to derive your private key from your public key, and sign transactions as if they were you. This is the thing to actually worry about.
Grover’s Algorithm (not the threat): Provides only a quadratic speedup for attacking hash functions like SHA-256 (Bitcoin mining). This sounds scary until you do the math.
A 2025 paper titled “Kardashev Scale Quantum Computing for Bitcoin Mining” calculated what Grover’s algorithm would actually require at Bitcoin’s real-world difficulty level:
~10²³ physical qubits (we currently have about 1,500)
~10²⁵ watts of power (the Sun produces ~3.8 × 10²⁶ watts)
To mine Bitcoin with a quantum computer, you would need roughly 3% of the Sun’s total energy output. We are a Kardashev Type 0.73 civilization. This is a Type II requirement.
For context: an “optimistically specified” quantum miner achieves about 13.8 GH/s. A single Antminer S21 does 200 TH/s. The classical ASIC is 14,500 times faster.
The stat to text your friend:Mining Bitcoin with a quantum computer would require 10²⁵ watts of power — roughly 3% of the Sun’s total energy output. The entire planet Earth currently uses about 1.8 × 10¹³ watts. You’d need to multiply humanity’s total energy consumption by a trillion to quantum-mine a single block.A $2,000 ASIC from Amazon is 14,500x faster than the best theoretical quantum miner. The quantum computer costs billions and needs to be cooled to near absolute zero. The ASIC plugs into a wall outlet.Quantum mining isn’t hard. It’s thermodynamically absurd.
Bottom line: Quantum mining is not a thing. Not now, not in 50 years, possibly not ever. If someone tells you quantum computers will “break Bitcoin mining,” they have confused two fundamentally different algorithms.
Part 3: The 8 Claims You’ll Hear (And Why 7.5 of Them Are Wrong)
Let me walk through the specific FUD claims in circulation and give you the counterargument for each. I’m using a half-point because one of these claims is half-right.
Claim 1: “All Bitcoin can be stolen overnight once quantum computers arrive”
Reality: Only Bitcoin with exposed public keys is vulnerable. Modern Bitcoin addresses (P2PKH, P2SH, SegWit) do not expose your public key until you spend from them. If you’ve never reused an address and never spent from it, your public key is not on the blockchain.
The breakdown:
Tier A (immediately vulnerable): ~1.7 million BTC in old P2PK format — keys visible right now
Tier B (vulnerable, but fixable): ~5.2 million BTC in reused addresses and Taproot — users can migrate
Tier C (briefly vulnerable): Every transaction is exposed during the ~10 minutes it sits in the mempool
Total: about 6.26 million BTC with exposed keys (Chaincode Labs estimate). That’s ~30-35% of the supply — significant, but not “all Bitcoin.”
Claim 2: “Satoshi’s coins will be stolen, crashing the market to zero”
Half-right: Satoshi’s ~1.1 million BTC are in P2PK format with exposed keys. They ARE among the most vulnerable coins. But:
Stealing them requires a machine that does not exist
Nation-states with early quantum capability would target intelligence and military systems — not attempt “what would be a very public Bitcoin theft PR stunt” (as the Quantum Canary research group puts it)
Building such a machine requires scaling from ~1,500 qubits to hundreds of thousands — a process that will take years of engineering, though the pace of that progress is genuinely uncertain
Claim 3: “Bitcoin can’t upgrade — it’s too slow and ungovernable”
False, but not without nuance. Bitcoin has successfully executed major upgrades:
SegWit (2015-2017) — Extremely contentious, near-failure, caused the Bitcoin Cash fork. But it shipped.
Taproot (2018-2021) — Smooth activation, ~3.5 years from proposal to live on mainnet.
BIP-360, the leading quantum-resistant proposal, was merged into Bitcoin’s BIP repository in early 2026. It introduces a new address type (bc1z) that removes Taproot’s quantum-vulnerable key-path spend. It’s in Draft status, with a testnet already running Dilithium post-quantum signature opcodes.
Ethan Heilman, BIP-360 co-author, estimates the full process at about 7 years: 2.5 years of development and review, 0.5 years for activation, and 4 years for ecosystem migration. He readily admits: “I’m just spitballing here. No one actually knows.”
The honest answer: Bitcoin can upgrade and has started, but the process is early-stage and needs to accelerate. The claim it’s “impossible” is false. The claim it’s “done” is also false.
Claim 4: “We only have 3-5 years”
Probably wrong, but not safely wrong. Expert estimates span a huge range:
Adam Back (Hashcash inventor, cited in Bitcoin whitepaper) — 20-40 years
Jensen Huang (NVIDIA CEO) — 15-30 years for useful quantum computers
Scott Aaronson (UT Austin, leading quantum complexity theorist) — refuses to give a timeline; notes breaking RSA would require “someone investing $100 billion”
Craig Gidney (Google Quantum AI) — 10% chance by 2030; also notes he does NOT see another 10x improvement in qubit estimates under current assumptions — the optimization curve may be flattening
Expert survey (26 quantum security researchers) — 28-49% chance within 10 years
Ark Invest — “Long-term, not imminent”
One thing worth understanding: Google’s Willow chip crossed the “below-threshold” barrier for quantum error correction in late 2024. This matters because it means that for each increment of error-correction code distance, the logical error rate drops by a constant factor (Lambda = 2.14 for Willow). That per-step improvement is exponential in error suppression — but the rate at which you can actually add those steps depends entirely on hardware scaling, which could be logarithmic, linear, or glacial. Below-threshold means scaling may now be possible. It does not mean scaling is fast, easy, or guaranteed.
Google also withheld its actual attack circuits from the March 2026 paper, publishing only zero-knowledge proofs. And Scott Aaronson has warned that at some point, researchers will stop publishing resource estimates for breaking cryptography. So the assumption that we’ll see Q-Day coming from a mile away is not guaranteed.
That said, building a machine with hundreds of thousands of fault-tolerant qubits remains an enormous engineering challenge. No quantum computer has ever factored a number larger than 13 digits. Breaking Bitcoin’s cryptography requires the equivalent of factoring ~1,300-digit numbers. That’s not a gap that closes overnight — but the trajectory deserves respect, not dismissal.
Claims 5-8: Quick Hits
“Quantum breaks mining” — No. Requires the Sun’s energy output. See Part 2.
“Harvest now, decrypt later” — Doesn’t apply to fund theft (blockchain is already public). Does apply to privacy (a legitimate but lesser concern).
“Google says 9 minutes” — Google says a theoretical circuit could run in 9 minutes on a 500,000-qubit machine that doesn’t exist. Google cautioned against FUD. Google withheld the attack circuits.
“Post-quantum crypto isn’t ready” — NIST has already standardized ML-KEM, ML-DSA, and SLH-DSA. The algorithms exist. The challenge is deploying them in Bitcoin, not inventing them.
Part 4: The Honest Part (What I Worry About)
A debunking article that dismisses everything loses credibility. Here are the five things that keep me up at night:
1. The qubit estimates have been collapsing — though the trend may be slowing. In 2012, breaking cryptography required an estimated 1 billion qubits. By 2019: 20 million. By 2025: under 1 million. In early 2026, Oratomic claimed feasibility with as few as 10,000 physical qubits using neutral-atom architecture — though it’s worth noting that all nine authors are Oratomic shareholders, and their estimate assumes a 101 physical-to-logical qubit ratio that has never been validated (the historical ratio is closer to 10,0001). It’s also worth noting that on neutral-atom hardware, the same computation that takes “9 minutes” on Google’s superconducting architecture would take 10-264 days — these are fundamentally different machines with fundamentally different speed profiles. And Gidney himself says the algorithmic optimization curve may be plateauing. Still, nobody knows when the “qubits needed” and “qubits available” lines cross. The honest answer is genuine uncertainty.
2. The exposed surface is growing, not shrinking. Taproot — Bitcoin’s newest and most promoted address format — exposes tweaked public keys on-chain, giving quantum attackers an indefinite offline window. Bitcoin’s most recent upgrade made things worse for quantum resistance. That’s an irony worth sitting with. And as others have pointed out, the problem extends beyond on-chain addresses — Lightning channels, hardware wallet connections, multisig setups, and xpub-sharing services all distribute public keys by design. In a world where a CRQC exists, “keep your public key private” isn’t realistic advice when entire systems are built around sharing them. BIP-360 is step one, not the whole answer.
3. Bitcoin’s governance is slow — but it has time. No soft fork has activated since November 2021 — over four years of base-layer stasis. Google targets 2029 for its own post-quantum migration. Bitcoin’s most optimistic estimate is 2033. Given how far away CRQCs likely are (most credible estimates range from 2040s to “possibly never”), this is not an emergency — but it’s not a reason for complacency either. The earlier preparation starts, the less rushed it needs to be.
4. Satoshi’s coins are an unsolvable game-theory problem. ~1.1 million BTC in P2PK addresses that can never be migrated because no one holds the keys (or Satoshi is absent). The options — do nothing, freeze, burn — all have serious consequences. There is no clean solution.
5. The blockchain is a permanent target list. Every exposed public key is catalogued forever at zero cost. Nation-states can prepare now and wait. Defense requires active coordination; attack requires only patience.
These are real challenges. But there’s another side worth hearing.
Why it might take much, much longer — or never happen at all. Serious physicists and mathematicians (not cranks) argue that fault-tolerant quantum computing at cryptographic scale faces barriers that may be fundamental, not merely engineering:
Leonid Levin (Boston University, co-inventor of NP-completeness): “Quantum amplitudes need accuracy to multi-hundredth decimals, but we have never seen a physical law valid to over a dozen decimals.” If nature doesn’t allow precision beyond ~12 decimal places, the entire QC enterprise hits a physics wall.
Michel Dyakonov (University of Montpellier, theoretical physicist): A 1,000-qubit system requires controlling ~10³⁰⁰ continuous parameters simultaneously — more than the number of subatomic particles in the universe. His assessment: “No, never.”
Gil Kalai (Hebrew University, mathematician): Argues that quantum noise exhibits irreducible correlations that worsen with system complexity, making error correction fundamentally impossible at scale. His conjectures are unproven after 20 years — but his experimental predictions have been partially wrong, which cuts both ways.
Tim Palmer (Oxford, physicist): His Rational Quantum Mechanics framework predicts a hard entanglement ceiling at roughly 1,000 qubits — well below cryptographic relevance.
These aren’t fringe positions. And the scoreboard favors them: the evidence to date strongly suggests that cryptographically relevant quantum computing is either vastly more difficult in practice than the theories predict, or entirely impossible due to some detail of the physical world we don’t yet understand. The autonomous driving analogy is apt: it works in demos, it attracts billions in investment, and it has been “5 years away” for over a decade.
The default assumption in most media coverage — that quantum computers will break cryptography and it’s just a matter of when — is not the conclusion the evidence supports. It’s the conclusion the hype cycle assumes.
Part 5: The Actual Reason to Upgrade (It’s Not Quantum)
Here’s the twist nobody talks about. (Credit to @reardencode for sharpening this point.)
Cryptographic systems broken by quantum computers to date: zero.
Cryptographic systems broken by classical mathematics to date: too many to count.
DES, MD5, SHA-1, RC4, SIKE, the Enigma machine — all fell to clever math, not quantum hardware. SIKE was a NIST post-quantum finalist that got destroyed in 2022 by a single researcher on a laptop in an hour. Classical cryptanalysis has been killing cryptographic systems for as long as cryptographic systems have existed.
secp256k1 — the elliptic curve Bitcoin uses — could fall to a mathematical breakthrough tomorrow. No quantum computer needed. Just a sufficiently clever number theorist with a new insight into the discrete logarithm problem. It hasn’t happened yet. But the history of cryptography is a history of systems that were “proven secure” until someone found a way through.
This is the actual reason Bitcoin should adopt alternate cryptographic schemes. Not because quantum computers are coming — they might never arrive. But because relying on a single cryptographic assumption for a $2 trillion network is exactly the kind of risk that serious engineering addresses proactively.
The quantum FUD is a distraction from this quieter, more real concern. And ironically, the work being done to prepare for quantum threats (BIP-360, post-quantum signatures, hash-based alternatives) also addresses the classical cryptanalysis risk. The right thing is being done, for the wrong reason. That’s fine — as long as it gets done.
Part 6: So What Should You Actually Do?
If you’re a Bitcoin holder:
Don’t panic. The threat is real but distant. You have time.
Stop reusing addresses. Every time you reuse an address, you expose your public key. Use fresh addresses for every receive.
Watch for BIP-360. When quantum-resistant address types become available, migrate your funds.
If you’re holding long-term, consider keeping funds in addresses you’ve never spent from. Your public key stays hidden.
Ignore the headlines. Read the actual papers. They’re more interesting and less scary than the coverage suggests.
If you’re a Bitcoin developer:
BIP-360 needs more reviewers. The testnet is running. The code needs eyeballs.
The 7-year timeline needs to compress. Every year of delay narrows the safety margin.
Start the governance conversation about legacy UTXOs. Satoshi’s coins won’t protect themselves. The community needs a plan.
If you’re someone who just read a scary headline:
Remember that 59% of shared links are never clicked. The headline is designed to make you feel something. The paper underneath is designed to make you think something. Go read the paper.
The Real Story
The quantum threat to Bitcoin is not a binary — it’s a spectrum. On one end: “Bitcoin is doomed and you should sell everything.” On the other: “Nothing to see here, quantum is a hoax.” Both ends are wrong.
The truth sits in a specific, actionable middle: Bitcoin has a real engineering challenge with known parameters, active development, and a timeline that is tight but manageable — if the community treats it with appropriate urgency.
The most dangerous thing isn’t quantum computers. It’s the media cycle that oscillates between panic and dismissal, making it impossible for anyone to think clearly about what is fundamentally a solvable problem.
Bitcoin has survived the block size wars, exchange hacks, regulatory assaults, and its own creator disappearing. It will survive quantum computing — but only if the community starts preparing now, not in a panic, but with the steady, methodical engineering focus that has always been Bitcoin’s greatest strength.
The house isn’t on fire. The house may never be on fire — at least not from the direction everyone’s pointing. But cryptographic assumptions don’t last forever. They never have. The right time to diversify your cryptographic foundations is before you need to, not after.
Bitcoin has always been built by people who prepare for threats that haven’t materialized yet. That’s not paranoia. That’s engineering.
#LearnToPrompt – try my wiki plugin llm-wiki.net
[Publishing from a flight, if you find something wrong i maybe take a little bit to fix it.]
Sources: 66 research documents across two topic wikis spanning quantum computing resource estimates, Bitcoin vulnerability analysis, debunking psychology, and content virality research. Key sources include Google Quantum AI (2026), Kardashev Scale Mining Paper (2025), BIP-360 documentation, Berger & Milkman (2012), the Debunking Handbook 2020, and practitioner accounts from Tim Urban, Dan Luu, and patio11. Full wiki available for peer review.




